Most voice agent tutorials get you to a demo. This one gets you to production. The difference is everything that happens when things go wrong - and in real-time voice systems, things go wrong constantly.
This freeCodeCamp guide walks through the architecture needed for a voice agent that can handle actual users, not just controlled demos. It's vendor-neutral, which means you can apply it regardless of which speech-to-text or LLM provider you're using. The principles stay the same.
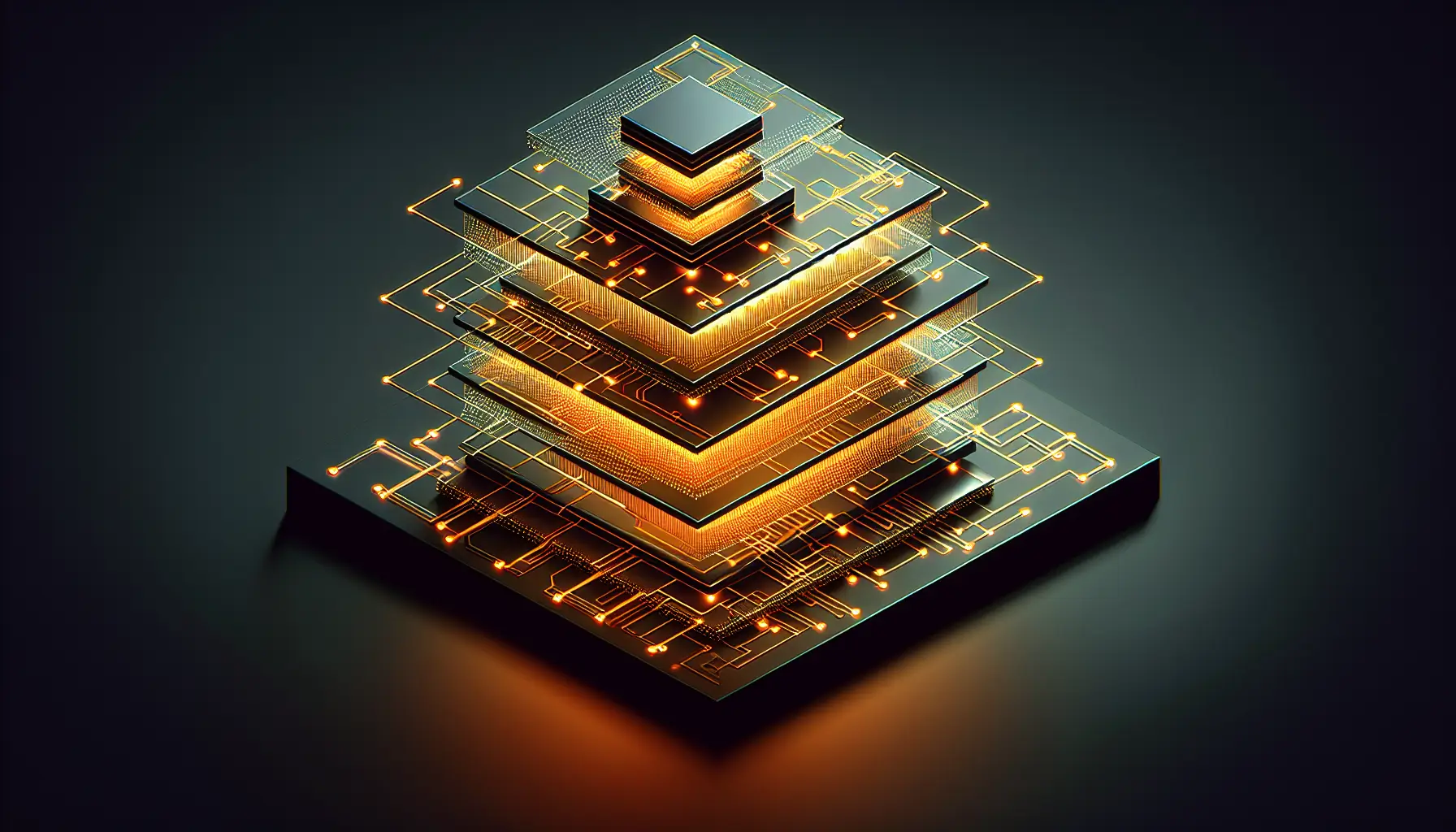
The Four-Layer Architecture
Production voice agents need four distinct systems working in concert. Token service - credentials stay server-side, never exposed to the client. WebRTC media layer - handles real-time audio streaming with the latency budgets that make conversation feel natural. Structured data channels - tool execution happens in a controlled environment, not through raw LLM output. Post-call processing - transcripts, analytics, and compliance logging happen after the call ends, not during it.
Each layer solves a different class of problem. The token service prevents credential leakage. WebRTC handles network instability and audio quality. Data channels let you execute tools safely without trusting LLM output directly. Post-call processing gives you visibility into what actually happened without slowing down the live interaction.
Why WebRTC, Not HTTP Streaming
Voice agents live or die on latency. HTTP streaming adds 200-500ms of overhead that users perceive as awkward pauses. WebRTC is designed for real-time media and includes adaptive bitrate streaming, jitter buffering, and packet loss recovery - all the things that make a voice call feel smooth instead of robotic.
Setting up WebRTC properly means handling STUN/TURN servers for NAT traversal, managing ICE candidates for connection negotiation, and dealing with browser permission models. The guide covers all of it. This is the stuff that doesn't work in demos but breaks in production.
Structured Data Channels - The Safety Layer
Here's the critical insight most tutorials miss: you cannot trust LLM output to execute tools directly. If your voice agent can book meetings, send emails, or update databases, you need a validation layer between the LLM's intent and the actual execution.
Structured data channels solve this. The LLM outputs a JSON schema describing what it wants to do. Your validation layer checks that schema against allowed operations, validates parameters, and only then executes the action. If the LLM hallucinates a tool call or suggests something outside its permissions, the validation layer catches it before anything breaks.
This isn't paranoia. It's operational reality. LLMs are probabilistic. They will occasionally output nonsense. Production systems need guardrails that assume this and handle it gracefully.
Latency Budgets and Where They Come From
A natural conversation has gaps of 200-300ms between turn-taking. Any longer and it feels like lag. Your voice agent has a latency budget of roughly 300ms from when the user stops speaking to when your response starts. That budget gets divided between: speech-to-text transcription, LLM inference, text-to-speech synthesis, and network transmission.
The guide breaks down realistic latency numbers for each component and shows where optimisation matters most. Spoiler: the LLM is usually the bottleneck. Streaming responses help, but you still need a model fast enough that the first tokens arrive within your budget. This is why model selection isn't just about accuracy - latency is a product requirement.
Post-Call Processing - The Unsexy Bit That Matters
Once the call ends, you need transcripts for compliance, analytics for improvement, and error logs for debugging. None of this should happen during the call - it adds latency and complexity. Instead, buffer everything in memory during the call, then flush it to storage afterward.
The guide covers structured logging patterns that make post-call analysis actually useful. Not just "here's a transcript," but "here's where the LLM struggled, here's where latency spiked, here's where the user had to repeat themselves." That's the data you need to improve the system.
For Anyone Building Voice Products
If you're building a voice agent, this guide is worth your time. It doesn't assume you're using a specific platform or vendor. It teaches the architectural patterns that apply regardless of your stack. Token management, WebRTC setup, data channel validation, and post-call processing are universal problems with known solutions.
The gap between demo and production in voice agents is larger than most other domains. Demos can fake latency by cherry-picking fast responses. Production can't. Demos don't need permission handling, error recovery, or compliance logging. Production does. This guide acknowledges that gap and shows you how to cross it.
Voice agents are becoming infrastructure. If you're building one, build it properly. This is how.